Make a WBS Chart showing the phases of creating a anti virus
software
Answers
Creating an antivirus software is a complex process that requires a lot of phases, to keep track of all these phases, a work breakdown structure (WBS) is used. A WBS is a visual representation of a project’s tasks that are broken down into smaller, more manageable components.
The WBS of an antivirus software development project might look like this:Phase 1: Research and AnalysisIn this phase, the developers carry out research to find out the latest threats and vulnerabilities. This is important to ensure that the antivirus software can handle new threats and zero-day attacks.Phase 2: DesignIn this phase, the developers create a detailed design of the software that outlines all the features and functionalities.
This phase is critical to ensure that all the requirements are met before the development phase starts.Phase 3: DevelopmentIn this phase, the developers start coding the software based on the design document. This phase is critical as it involves creating the core functionality of the antivirus software.Phase 4: Testing and DebuggingIn this phase, the developers test the software to identify any bugs or errors that need to be fixed. This phase is critical to ensure that the software is robust and can handle all types of threats.Phase 5: DeploymentIn this phase, the developers deploy the antivirus software on the target platform.
This phase is critical to ensure that the software is installed correctly and is running smoothly.Phase 6: MaintenanceIn this phase, the developers monitor the software to ensure that it is working as expected. This phase is critical to ensure that any issues that arise are fixed promptly and that the software remains up-to-date.
To know more about Software visit :
https://brainly.com/question/32393976
#SPJ11
Related Questions
Please please help I don’t understand

Answers
Answer:
ask for the user's age
Explanation:
you always input the values of a variable before you begin any processes
categorical data _____.
a. indicate either how much or how many
b. are always numeric
c. may be either numeric or nonnumeric
d. are always nonnumeric
Answers
Data with categories might be either numerical or non-numerical.
Do categorical data have a quantitative value or not?Categorical data are by definition non-numerical, although they can still be presented and examined using numbers. Although the information value of categorical data is far lower than that of numerical data, nearly no study would be complete without considering the results of their analysis.
Are categorical data never numerical?Categorical data can be calculated in numerical values even though it is qualitative data. These potential values, however, lack quantitative characteristics, making it impossible to make any calculations from them. Depending on its type, categorical data can also be divided into binary and nonbinary categories.
To know more about Data visit:-
https://brainly.com/question/13650923
#SPJ1
How do I convert years to days on Python. For example, if I were to enter 3 years it should output "You are 1095 days old".
Answers
years = int(input("Enter the # of years: "))
print("You are "+str(years*365)+" days old")
I wrote the code in python 3.8. I hope this helps!
Determine if the following problems exhibit task or data parallelism:
•Using a separate thread to generate a thumbnail for each photo in a collection
•Transposing a matrix in parallel
•A networked application where one thread reads from the network and another
writes to the network
•The fork-join array summation application described in Section 4.5.2
•The Grand Central Dispatch system.
Answers
In Computer technology, parallelism can be defined as a situation in which the execution of two (2) or more different tasks starts at the same time. Thus, it simply means that the two (2) tasks or threads are executed simultaneously and as such making computation faster.
The types of parallelism.Generally, there are two (2) main types of parallelism that is used in computer programming and these are:
Data parallelismTask parallelismRead more on parallelism here: https://brainly.com/question/20723333
What is the command to list the top 10 files that use the most disk space in linux?
Answers
Type du -a /dir/ | sort -n -r | head -n 20. du will calculate the file space used. The sort will sort out the output of a du command.
Why is Linux used? Linux is an open source operating system (OS). An operating system, which is a piece of software, is directly in charge of managing the hardware and resources of a system, including the CPU, memory, and storage. By sitting between applications and hardware, the operating system (OS) creates connections between all of your software and the operational physical resources. Many of the gadgets you likely own, such as Android smartphones, tablets, and Chromebooks, as well as digital storage, cameras, wearable technology, personal video recorders, and more, all support Linux. Your automobile has Linux running on the inside. Linux is an open-source alternative to Windows OS, which is a for-profit operating system.To learn more about Linux, refer to:
https://brainly.com/question/25480553
#SPJ4
the revocation status of the smart card certificate used for authentication could not be determined
Answers
This shows that the domain controllers are unable to determine the Certificate Revocation List (CRL) server is offline or unavailable, respectively (CRL).
Exactly how do I activate smart card authentication?Get the certificate chain from the CA that supplies smart card certificates. Set AD as the Identity Provider by importing the CA into SecureW2. By entering the user's login information and AD policy information, administrators can create customized certificates for individual users.
A smart card error—how do I solve it?You can restart the computer or try adding the device once more to get rid of this problem notice. The failure of the smart card service is indicated by this internal, unrecoverable error.
To know more about CRL visit :-
https://brainly.com/question/28269802
#SPJ4
Identify the marketing relationship that the given scenario portrays. Matt’s band has released their first independent album at their own expense. They are planning a short tour in the Northwest of the United States, but they need transportation. Matt’s van is falling apart, so he is thinking about approaching a local dealership. Matt is looking for ___ . Quick please
Answers
Answer: the answer should be false pretense.
identify the major issues in implementing computerized support systems
Answers
Implementing computerized support systems can be accompanied by several major issues. These include technical challenges, resistance to change, data security and privacy concerns, integration with existing systems, user training and adoption, and ongoing maintenance and support requirements.
1. Technical Challenges: Implementing computerized support systems may involve complex technical aspects such as system compatibility, integration with existing infrastructure, scalability, and reliability. Ensuring smooth implementation and addressing technical issues can be a significant challenge.
2. Resistance to Change: Introducing new computerized support systems often encounters resistance from employees who may be accustomed to traditional methods. Resistance to change can hinder adoption and affect the success of implementation. Proper change management strategies, effective communication, and user involvement are crucial to address this issue.
3. Data Security and Privacy Concerns: Computerized support systems involve handling sensitive data, which raises concerns about data security and privacy. Implementing robust security measures, compliance with regulations, and establishing strict access controls are essential to mitigate these risks.
4. Integration with Existing Systems: Integrating computerized support systems with existing systems and processes can be complex and time-consuming. Ensuring seamless data flow, interoperability, and compatibility are critical for successful implementation.
5. User Training and Adoption: Adequate training and support for users are crucial to ensure smooth adoption and utilization of the computerized support systems. Insufficient training or resistance to learning new technologies can hinder the system's effectiveness.
6. Ongoing Maintenance and Support: Computerized support systems require ongoing maintenance, updates, and technical support to address issues, ensure system performance, and incorporate enhancements. Establishing a proper support structure and allocating necessary resources is essential for long-term success.
By addressing these major issues during the implementation phase, organizations can increase the chances of successful adoption and maximize the benefits of computerized support systems.
learn more about computerized support systems here
https://brainly.com/question/32481248
#SPJ11
which statements compares the copy and cut commands
Answers
The statement that accurately compares the copy and cut commands is 2)Only the cut command removes the text from the original document.
When using the copy command, the selected text is duplicated or copied to a temporary storage area called the clipboard.
This allows the user to paste the copied text elsewhere, such as in a different location within the same document or in a separate document altogether.
However, the original text remains in its original place.
The copy command does not remove or delete the text from the original document; it merely creates a duplicate that can be pasted elsewhere.
On the other hand, the cut command not only copies the selected text to the clipboard but also removes it from the original document.
This means that when the cut command is executed, the selected text is deleted or "cut" from its original location.
The user can then paste the cut text in a different place, effectively moving it from its original location to a new location.
The cut command is useful when you want to relocate or remove a section of text entirely from one part of a document to another.
For more questions on cut commands
https://brainly.com/question/19971377
#SPJ8
Question: Which statement compares the copy and cut commands?
1. only the copy command requires the highlighting text
2. only to cut command removes the text from the original document
3. only the cut command uses the paste command to complete the task
4. only the copy command is used to add text from a document to a new document
Authentication is concerned with determining _______.
Answers
Authentication can be described as the process of determining whether someone or something is, in fact, who or what it says it is. Authentication technology serves us to access control for systems by checking to see if a user's credentials match the credentials in a database of authorized users or in a data authentication server.
There are three basic kind of authentication. The first is knowledge-based — something like a password or PIN code that only the identified user would know. The second is property-based, meaning the user possesses an access card, key, key fob or authorized device unique to them. The third is biologically based.
You can learn more about authentication at https://brainly.com/question/28398310
#SPJ4
Given the following code, which is the correct output?
int n = 14; do { cout << n << " "; n = n-3; } while (n>=2);
Group of answer choices 11 8 5 2 11 8 5 2 -1 14 11 8 5 14 11 8 5 2 14 11 8 5 2 -1
Answers
The correct output of the given code will be "14 11 8 5 2".The code uses a do-while loop to repeatedly execute the block of code inside the loop. The loop starts with an initial value of n = 14 and continues as long as n is greater than or equal to 2.
Inside the loop, the value of n is printed followed by a space, and then it is decremented by 3.The loop will execute five times, as the condition n>=2 is true for values 14, 11, 8, 5, and 2. Therefore, the output will consist of these five values separated by spaces: "14 11 8 5 2".
Option 1: 11 8 5 2 - This option is incorrect as it omits the initial value of 14.Option 2: 11 8 5 2 - This option is correct and matches the expected output.Option 3: 14 11 8 5 - This option is incorrect as it omits the last value of 2.Option 4: 14 11 8 5 2 -1 - This option is incorrect as it includes an extra -1 which is not part of the output.Option 5: 14 11 8 5 2 - This option is incorrect as it includes an extra 14 at the beginning.Therefore, the correct output of the given code is "14 11 8 5 2".
Learn more about loop here:- brainly.com/question/14390367
#SPJ11
Select the correct answer.
An Al scientist placed an agent in a known environment. The agent observed changes in the environment. Soon, it began to take action
toward making a decision. What was the agent doing?
A. offline computation
B. online computation
OC. learning
OD. perceiving
Answers
According to the given condition, the agent doing the process of perceiving. Thus the correct answer is D.
What is perceiving?Perceiving refers to the implementation of any concept based on learning, understanding, and observation of skills to make effective decisions.
In this situation, the agent has observed changes in the environment and based on his observation and analysis began to take action for decision making.
These perceiving nature helps to enhance the process of learning to seek improvement.
Therefore, option D reflects the perceiving nature of agent.
Learn more about skills, here:
https://brainly.com/question/9648460
#SPJ1
Can someone help me ?

Answers
Answer:
yes please
Explanation:
5 evaluation criteria
Answers
Answer:
relevance, efficiency, effectiveness, impact and sustainability.
Consider the following instance variables and method from a class: private String descriptor; public String makeSentence(int quant, boolean sign) { String s = "Object is "; if (!sign) { s += "not "; } for (int i = 0; i < quant; i++) { s += "very "; } return s + descriptor; } Suppose an object of this class is initialized so the value of descriptor is "regular". What would be returned by the call makeSentence(3, false) made on this object?
Answers
The call makeSentence(3, false) will return
"Object is not very very very regular"
The program fragment is:
///////////////////////////////////////////////////////////////////////////////////////////////////////////////
private String descriptor;
public String makeSentence(int quant, boolean sign) {
String s = "Object is ";
if (! sign) {
s += "not ";
}
for (int i = 0; i < quant; i++) {
s += "very ";
}
return s + descriptor;
}
///////////////////////////////////////////////////////////////////////////////////////////////////////////////
descriptor is an instance field of the class. When makeSentence(3, false) is called, it does the following;
Initializes a local variable s with "Object is "
s now contains "Object is "
Since sign== false, the if block executes
s now contains "Object is not "
The for loop will execute 3 times to append "very " to s
s now contains "Object is not very very very "
Finally the return statement returns a concatenation of the contents of descriptor (descriptor=="regular") and s
s now contains "Object is not very very very regular"
Learn more about programs here: https://brainly.com/question/19625875
Alisa Miller claims that today's college graduates:
Answers
Answer: know less about the world then there counterparts
Explanation:
Answer:
know less about the world then there counterparts
Explanation:
windows defender is antimalware software built-in to microsoft operating systems. true or false
Answers
True, Windows Defender is an antimalware software built in to Microsoft operating system.
Antimalware software, also known as antivirus software, is a type of software designed to protect computer systems from malware, which includes viruses, spyware, adware, and other malicious software. Antimalware software works by scanning files and software programs for known malware signatures and behavior patterns and then quarantining or deleting any identified threats. Antimalware software also includes real-time protection, which monitors the system for suspicious activity and prevents malware from infecting the system in the first place. Some antimalware software also includes additional features, such as firewalls, parental controls, and password managers. Antimalware software is an essential component of computer security, as malware can cause significant damage to computer systems, steal sensitive information, and compromise user privacy.
Learn more about antimalware software here:
https://brainly.com/question/29975689
#SPJ11
Windows Defender is an antimalware software built-in to the Microsoft operating system. True.
Explaination:
True, Windows Defender is an antimalware software built in to Microsoft operating system.
Antimalware software, also known as antivirus software, is a type of software designed to protect computer systems from malware, which includes viruses, spyware, adware, and other malicious software. Antimalware software works by scanning files and software programs for known malware signatures and behavior patterns and then quarantining or deleting any identified threats. Antimalware software also includes real-time protection, which monitors the system for suspicious activity and prevents malware from infecting the system in the first place. Some antimalware software also includes additional features, such as firewalls, parental controls, and password managers. Antimalware software is an essential component of computer security, as malware can cause significant damage to computer systems, steal sensitive information, and compromise user privacy.
Learn more about antimalware software here:
brainly.com/question/29975689
#SPJ11
Which of the following shows the assignment of a string to a variable? Select 3 options.
answer = input("How old are you? ")
answer = "23"
answer = '23'
answer = 23
answer = (23)
Answers
Answer:
23, (23)
Explanation:
Answer:
⬇️
Explanation:
answer = "23"
answer = input("How old are you? ")
answer = '23'
correct on edg. 2021
Name the substance you think is in the cylinder that you cannot see and prevents the plunger from going all the way in even when you push the plunger hard
Answers
The substance I think is in the cylinder that you cannot see and prevents the plunger from going all the way in even when you push the plunger hard is Air.
What do you feel as when one push the plunger?When a person push on the plunger, the person can feel the air pushing it back. When a person has stop pushing, the air inside the syringe will tend to return to its normal size.
Note that there are a lot of ways to compress air. A person can do so by squeezing a specified volume of air into a smaller space.
Learn more about cylinder from
https://brainly.com/question/26806820
Proportional spacing replaced what other kind of spacing? question 2 options: parallel spacing monospacing one-to-one spacing fixed spacing
Answers
According to the statement, Proportional spacing replaced monospacing.
Describe monospacing.A monospaced font is one in which each letter and character takes up the same amount of horizontal space. It is also known as a fixed-pitch, fixed-width, or non-proportional font. Variable-width fonts, in contrast, feature letters and spacing that are all the same width.
Monospace fonts have their uses.Practicality: On all screen sizes, monospaced typefaces are exceptionally simple to read. This means that your clients can quickly and easily locate what they're looking for on any device, greatly enhancing the user experience. Your users may become clients more frequently as a result.
To know more about monospace visit :
https://brainly.com/question/17824852
#SPJ4
A student wants an algorithm to find the hardest spelling word in a list of vocabulary. They define hardest by the longest word.
Implement the findLongest method to return the longest String stored in the parameter array of Strings named words (you may assume that words is not empty). If several Strings have the same length it should print the first String in list with the longest length.
For example, if the following array were declared:
String[] spellingList = {"high", "every", "nearing", "checking", "food ", "stand", "value", "best", "energy", "add", "grand", "notation", "abducted", "food ", "stand"};
The method call findLongest(spellingList) would return the String "checking".
Use the runner class to test this method: do not add a main method to your code in the U6_L3_Activity_One.java file or it will not be scored correctly.
Hint - this algorithm is very similar to the algorithms you have seen to find maximum/minimum values in unit 4. You need a variable which will keep track of the longest word in the array (either directly or as the array index of that word). Start this variable off with a sensible value, update it whenever a longer word is found, then return the longest word at the end.
Answers
Answer:
Initialize the “longest word” by an empty string and update it when a longer word is found
Explanation:
import java.util.stream.Stream;
public static String findLongest(String[] spellingList) {
return Stream.of(spellingList).reduce("", (longestWord, word) -> (
longestWord.length() < word.length() ? word : longestWord
));
}
If your company increases its market penetration, what is happening?
A.
The target market is growing.
B.
More people in the target market are buying the company's product.
C.
The market saturation of the target market has decreased.
D.
Competitors who offer similar products are entering the market.
D.
Your company collects credit card information from customers.
Answers
Answer: (A, B, E)
A. ) The target market is growing.
B. ) More people in the target market are buying the company's product.
E. ) Your company collects credit card information from customers.
Explanation: Simply what was on the assignment. Correct on Edge.
I hope this helped!
Good luck <3
Answer:
a,b,e like the top one said
Explanation:
this is late but thats okay
Question: What is the answer to Codehs 2.5.7 Circle Pyramid
Whoever has the CORRECT answer will get 25 points!! and marked the brainliest!!
Answers
Answer:
4
Explanation:
trust me man
The Codehs Python Circle Pyramid. Yes, this is the answer
What is Pyramid?The Pyramid is a large, triangular-shaped building that has four steep sides that meet at a point at the summit and often a flat base. Many various cultures, including Ancient Egypt, Mesoamerica, and China, have erected pyramids all over the world. Ancient Egyptian pyramids, which served as tombs for pharaohs and their families, are the most well-known examples of pyramid architecture.
Yes, this is the answer:
import from turtle
# Set up your starting position and screen.
setup(500,300)
setworldcoordinates(-250,-150,250,150)
penup()
home()
# Make a pyramid.
pendown()
in range(4) for i:
circle(25,360)
left(90)
forward(50)
# Protect your turtle.
hideturtle()
# Window closes upon click.
exitonclick()
Learn more about Pyramid, here:
brainly.com/question/5017673
#SPJ2
Your question is incomplete, most probably the complete question is:
Does anybody have the answer to Exercise 2.5.7: Circle Pyramid for codehs python?
Over the weekend, i was thinking about the process for analyzing the technology needs for this new department. the service department will need a system to support its unique needs of scheduling technicians, obtaining parts for repair, and setting up follow up appointments once parts are in-stock. i want to make sure that none of the analysis and design tasks fall through the cracks. i need you to identify all of the tasks that you will need to complete. i find it is helpful to create a work breakdown structure to identify the tasks. don't forget to include the system and industry analysis, system design, implementation plans, and security tasks in your wbs. what would be an example of a wbs?
Answers
The primary problem to be attained is the estimating of the sources. Its it good that one assign sources to all of the activity as in step with the things that can be done of that pastime and those to be finished efficiently as well as successfully.
What is WBS?The term Work Breakdown Structure (WBS) is known to be a form of an hierarchical statement of the tasks that is needed to complete a project.
Note that the WBS tends to “breaks down” the structure of a project into what we call the manageable deliverables.
The Work breakdown structure (WBS) in project management is also known as a method for finishing a complex, multi-step project and as such, The primary problem to be attained is the estimating of the sources. Its it good that one assign sources to all of the activity as in step with the things that can be done of that pastime and those to be finished efficiently as well as successfully.
Learn more about Work Breakdown Structure from
https://brainly.com/question/3757134
#SPJ1
if you send a tracked email to a contact and you get a notification saying they read it, when should you call them?
Answers
One should call the contact after allowing them sufficient time to respond to the email.
If you have sent a tracked email to a contact and received a notification that they have read it, it is important to give them adequate time to respond before making a follow-up call. The appropriate amount of time may vary depending on the nature of the email and the relationship with the contact, but it is generally recommended to wait at least a few days. This allows the contact time to review the email and formulate a response.
However, it is also important not to wait too long to make the follow-up call, as the contact may have forgotten about the email or moved on to other tasks. As a general rule, it is best to make the follow-up call within a week or so of sending the email, depending on the urgency of the matter. When making the call, it is helpful to reference the email and ask if the contact has had a chance to review it and if they have any questions or concerns. By allowing sufficient time for a response and making an appropriate follow-up call, you can increase the likelihood of a successful outcome.
You can learn more about email at
https://brainly.com/question/29515052
#SPJ11
in order to make a virtual machine perform better, take this step after installing a guest os.
Answers
To make a virtual machine perform better after installing a guest OS, you should allocate more resources, such as RAM and CPU cores, to the virtual machine.
To make a virtual machine perform better, follow the given steps :
1. Power off the virtual machine if it is currently running.
2. Open the virtual machine software you are using (e.g., VMware, VirtualBox).
3. Select the virtual machine you want to improve performance for.
4. Locate the settings or configuration options for the virtual machine.
5. In the settings, find the section for system resources, which may be under "System" or "Hardware."
6. Increase the amount of RAM and/or CPU cores allocated to the virtual machine. Be mindful not to allocate too much of your host system's resources, as it may negatively affect the host system's performance.
7. Save the changes and restart the virtual machine.
By allocating more resources to the virtual machine after installing a guest OS, you can improve its performance.
To learn more about a virtual machine visit : https://brainly.com/question/28901685
#SPJ11
Please Help! (Language=Java) This is due really soon and is from a beginner's computer science class!
Assignment details:
CHALLENGES
Prior to completing a challenge, insert a COMMENT with the appropriate number.
1) Get an integer from the keyboard, and print all the factors of that number. Example, using the number 24:
Factors of 24 >>> 1 2 3 4 6 8 12 24
2) A "cool number" is a number that has a remainder of 1 when divided by 3, 4, 5, and 6. Get an integer n from the keyboard and write the code to determine how many cool numbers exist from 1 to n. Use concatenation when printing the answer (shown for n of 5000).
There are 84 cool numbers up to 5000
3) Copy your code from the challenge above, then modify it to use a while loop instead of a for loop.
5) A "perfect number" is a number that equals the sum of its divisors (not including the number itself). For example, 6 is a perfect number (its divisors are 1, 2, and 3 >>> 1 + 2 + 3 == 6). Get an integer from the keyboard and write the code to determine if it is a perfect number.
6) Copy your code from the challenge above, then modify it to use a do-while loop instead of a for loop.
Answers
Answer:
For challenge 1:
import java.util.Scanner;
public class Main {
public static void main(String[] args) {
// Get an integer from the keyboard
Scanner scanner = new Scanner(System.in);
System.out.print("Enter an integer: ");
int num = scanner.nextInt();
// Print all the factors of the integer
System.out.print("Factors of " + num + " >>> ");
for (int i = 1; i <= num; i++) {
if (num % i == 0) {
System.out.print(i + " ");
}
}
}
}
For challenge 2:
import java.util.Scanner;
public class Main {
public static void main(String[] args) {
// Get an integer from the keyboard
Scanner scanner = new Scanner(System.in);
System.out.print("Enter an integer: ");
int n = scanner.nextInt();
// Count the number of cool numbers from 1 to n
int coolCount = 0;
for (int i = 1; i <= n; i++) {
if (i % 3 == 1 && i % 4 == 1 && i % 5 == 1 && i % 6 == 1) {
coolCount++;
}
}
// Print the result using concatenation
System.out.println("There are " + coolCount + " cool numbers up to " + n);
}
}
For challenge 3:
import java.util.Scanner;
public class Main {
public static void main(String[] args) {
// Get an integer from the keyboard
Scanner scanner = new Scanner(System.in);
System.out.print("Enter an integer: ");
int n = scanner.nextInt();
// Count the number of cool numbers from 1 to n using a while loop
int coolCount = 0;
int i = 1;
while (i <= n) {
if (i % 3 == 1 && i % 4 == 1 && i % 5 == 1 && i % 6 == 1) {
coolCount++;
}
i++;
}
// Print the result using concatenation
System.out.println("There are " + coolCount + " cool numbers up to " + n);
}
}
For challenge 5:
import java.util.Scanner;
public class Main {
public static void main(String[] args) {
// Get an integer from the keyboard
Scanner scanner = new Scanner(System.in);
System.out.print("Enter an integer: ");
int num = scanner.nextInt();
// Determine if the integer is a perfect number
int sum = 0;
for (int i = 1; i < num; i++) {
if (num % i == 0) {
sum += i;
}
}
if (sum == num) {
System.out.println(num + " is a perfect number.");
} else {
System.out.println(num + " is not a perfect number.");
}
}
}
For challenge 6:
import java.util.Scanner;
public class Main {
public static void main(String[] args) {
// Get an integer from the keyboard
Scanner scanner = new Scanner(System.in);
System.out.print("Enter an integer: ");
int num = scanner.nextInt();
// Determine if the integer is a perfect number using a do-while loop
int sum = 0;
int i = 1;
do {
if (num % i == 0) {
sum += i;
}
i++;
} while (i < num);
if (sum == num) {
System.out.println(num + " is a perfect number.");
} else {
System.out.println(num + " is not a perfect number.");
}
}
}
Create a C++ program using arithmetic operators to compute the AVERAGE of THREE (3) QUIZZES and display the score and average on different lines.
The output should be similar to this:
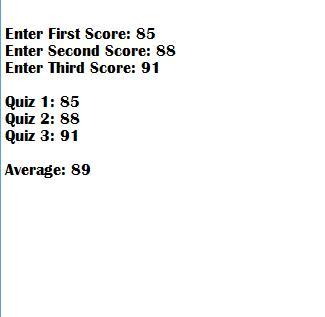
Answers
using the knowledge in computational language in python it is possible to write a code that using arithmetic operators to compute the average of three quizzes and display the score and average on different lines.
Writting the code:#include <iostream>
using namespace std;
int main()
{
float n1,n2,n3,n4,tot,avrg;
cout << "\n\n Compute the total and average of four numbers :\n";
cout << "----------------------------------------------------\n";
cout<<" Input 1st two numbers (separated by space) : ";
cin>> n1 >> n2;
cout<<" Input last two numbers (separated by space) : ";
cin>> n3 >> n4;
tot=n1+n2+n3+n4;
avrg=tot/4;
cout<<" The total of four numbers is : "<< tot << endl;
cout<<" The average of four numbers is : "<< avrg << endl;
cout << endl;
return 0;
}
See more about C++ at brainly.com/question/19705654
#SPJ1

Use the drop-down menus to complete the steps for filtering records in a form.
1. Open the (1) tab.
3. In the Sort & Filter group, click (2), and click Filter by Form.
4. Enter or select a value to set the filter.
5. On the Home tab, in the Sort & Filter group, click the (3) button to toggle the filter.
1= create, database tools, file, home
2= advanced, filtering, find, new
3= ascending, descending, apply filter, toggle filter
Answers
Answer:
Home, advanced, apply filter
Explanation:
edge 2021
In the completion of the steps for filtering records, one can:
Open the Home tab.click (advanced), and click Filter by Form.click the (apply filter ) button to toggle the filter. What is filtering of records?Filtering is know to be a very vital methods that is used to see only the data that a person want to be shown in Access databases.
Conclusively, By following the steps above, one can achieving the filtering of the records that they desires.
Learn more about filtering records from
https://brainly.com/question/22238933
#SPJ1
what is the meaning of .net in computer
Answers
Answer:
.net is a top-level domain, also known as a TLD. Derived from the word network, it was originally developed for companies involved in networking technology. Today .net is one of the most popular domain names used by companies all over the world to launch their business online.